Centos 7 Generate Ssh Host Keys
Mar 28, 2020 Configure SSH Host Based Authentication using sshdconfig, shosts,equiv per user RHEL/CentOS 7/8. Compare Host based authentication vs public key authentication. Mar 28, 2020 More details on SSH Public Key Authentication (with and without password) in Linux. My Lab Environment. I am using RHEL 7 and 8 Linux hosts to configure Host based authentication. Here rhel-7 will be my client using which I will initiate the SSH connection while rhel-8 will act as a server. root@rhel-7 # cat /etc/hosts 127.0.0.1 localhost localhost.localdomain localhost4 localhost4. When working with a CentOS server, chances are you will spend most of your time in a terminal session connected to your server through SSH. In this guide, we’ll focus on setting up SSH keys for a CentOS 8 server. SSH keys provide a straightforward, secure method of logging into your server and are recommended for all users. Jun 09, 2018 Most Linux and Unix distribution create ssh keys for you during the installation of the OpenSSH server package. But it may be useful to be able re-generate new server keys from time to time. For example, when you duplicate VM (KVM or container) which contains an installed ssh package and you need.
- Centos 7 Generate Ssh Host Keys On Mac
- Centos 7 Generate Ssh Host Keys On Computer
- Centos 7 Ssh Key Authentication
- Centos 7 Generate Ssh Host Keys Download
- Install / Initial Config
- NTP / SSH Server
- DNS / DHCP Server
- Storage Server
- Virtualization
- Cloud Compute
- (15) Configure Horizon
- Container Platform
- Directory Server
- WEB Server
- Database
- Redis
- MySQL 8.0
- PostgreSQL 12
- MariaDB 10.3
- SQL Server 2019
- Oracle Database 19c
- FTP / Samba / MAIL
- Proxy / Load Balancer
- Monitoring
- Monitorix
- OSQuery
- MRTG
- Cacti
- Munin
- Sensu
- Nagios
- SysStat
- Zabbix 4.2
- Zabbix 4.0 LTS
- Lang / Development
- CUDA
- TensorFlow
- Scala
- Ruby
- Node.js
- PHP
- Python
- .NET Core
- Java
- Desktop Environment
- Others #1
- Zarafa - Groupware
- Zimbra - Groupware
- Bacula - Backup
- Subversion - Revision Control
- Gitolite3 - Revision Control
- RabbitMQ - Message Broker
- Memcached - Memory Cache
- ElasticStack - Search Engine++
- Func - Remote Manage
- Salt - Config Manage
- Puppet - Config Manage
- Ansible - Config Manage
- Spacewalk - System Manage
- Pacemaker - HA Cluster
- PXE Boot- PXE Server
- OpenVPN - VPN Server
- LVM - LVM Manage
- Rsyslog - Syslog Server
- Cgroups - Resource Control
- Auditd - System Audit
- SELinux - Access Control
- Firewalld - Packet Filter
- Others #2
SSH keys can serve as a means of identifying yourself to an SSH server using public-key cryptography and challenge-response authentication. The major advantage of key-based authentication is that in contrast to password authentication it is not prone to brute-force attacks and you do not expose valid credentials, if the server has been compromised.
Furthermore SSH key authentication can be more convenient than the more traditional password authentication. When used with a program known as an SSH agent, SSH keys can allow you to connect to a server, or multiple servers, without having to remember or enter your password for each system.
Key-based authentication is not without its drawbacks and may not be appropriate for all environments, but in many circumstances it can offer some strong advantages. A general understanding of how SSH keys work will help you decide how and when to use them to meet your needs.
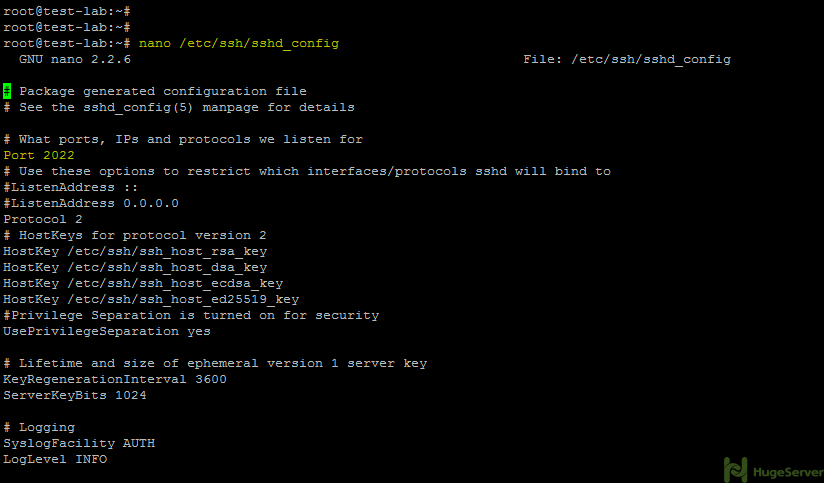
In this guide, we’ll set up SSH keys for a CentOS 7
Generate a Key Pair
. Normally this happens when SSH keys don’t get generated on the startup. If your system is compromised and your keys are stolen and you want to generate new keys. There could be some other reasons also but if you are reading this article then i believe you already have some reason with you. Generating Host Keys. Aug 19, 2019 1. Using the SSH keys, log into the remote CentOS server which has administrative privileges: ssh username@remotehost. Next, open the SSH daemon configuration file using a text editor of your choice: sudo nano /etc/ssh/sshdconfig. Look for the following line in the file: PasswordAuthentication yes. Apr 18, 2018 In this tutorial, we'll focus on setting up SSH keys for a vanilla CentOS 7 installation. SSH keys provide a straightforward, secure way of logging into your server and are recommended for all users. By default, ssh-keygen will create a 2048-bit RSA key pair, which is.
- Open Terminal
You now have a public and private key that you can use to authenticate. The next step is to place the public key on your server so that you can use SSH-key-based authentication to log in.
Upload your Public Key
There are a few different ways to upload your public key
1. Using ssh-copy-id
ssh-copy-id is a utility available on some operating systems that can copy a SSH public key to a remote server over SSH.
Now try logging into the machine, with: “ssh ‘[email protected]remote_host‘ “ and check to make sure that only the key(s) you wanted were added.
2. Using Secure Copy (scp)
Secure Copy (scp) is a tool that copies files from a local computer to a remote server over SSH
Connect to your server via SSH with the user you would like to add your key to:
Create the ~/.ssh directory and authorized_keys file if they don’t already exist:
Centos 7 Generate Ssh Host Keys On Mac
Give the ~/.ssh directory and authorized_keys files appropriate file permissions:
In terminal on your local machine, use scp to copy the contents of your SSH publickey(id_rsa.pub) into the authorized_keys file on your server.
Now you can log in to the server with your key.
3. Copying Public Key Manually
If you do not have password-based SSH access to your server available, you will have to complete the above process manually.
We will manually append the content of your id_rsa.pub file to the ~/.ssh/authorized_keys file on your remote machine.
To display the content of your id_rsa.pub key, type this into your local computer:
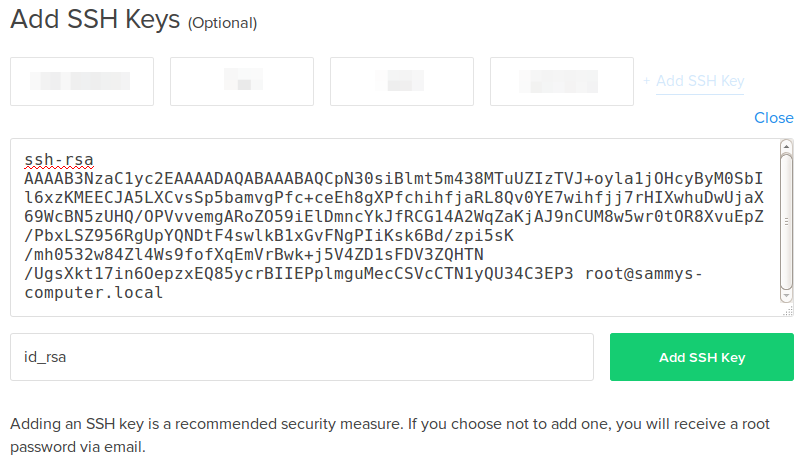
Note that the public key begins with ssh-rsa and ends with [email protected]
Centos 7 Generate Ssh Host Keys On Computer
Copy that text, connect to your server via SSH with the user you would like to add your key to:
Create the~/.ssh directory and authorized_keys file if they don’t already exist:
Give the ~/.ssh directory and authorized_keys files appropriate file permissions:
Open the authorized_keys file with the text editor. Then, paste the contents of your public key that you copied in step one on a new line at the end of the file. Save and close the file.
Napoleon total war key generator 2. Now you can log in to the server with your key.
Centos 7 Ssh Key Authentication
Creating SSH shortcuts
Instead of using SSH on an IP address that you’ll definitely forget, you can use shortcuts instead
Add an entry for each computer you want to connect to, like this:
Now, you can ssh into the server with the shortcut.
You should now have SSH-key-based authentication configured on your server, allowing you to sign in without providing an account password.