What Generates The Key Pair Used In Asymmetric Cryptography
Learn what Asymmetric Encryption is, how it works, and what it does
- What Generates The Key Pair Used In Asymmetric Cryptography In Math
- What Generates The Key Pair Used In Asymmetric Cryptography Theory
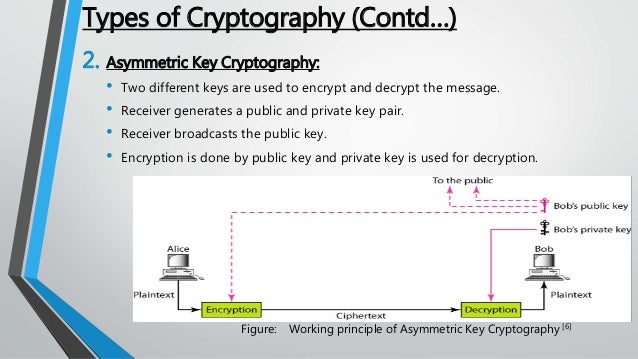
The two participants in the asymmetric encryption workflow are the sender and the receiver. First, the sender obtains the receiver's public key. Then the plaintext is encrypted with the asymmetric encryption algorithm using the recipient's public key, creating the ciphertext. Asymmetric cryptography also known as public-key encryption uses a public/private key pair to encrypt and decrypt data. Public key in asymmetric cryptography is available to public but the private key must be protected with the user, else it can be used to decrypt data.
This is part 3 of using Public Key Infrastructure (PKI) and Private Key Cryptography for your Windows Server 2012 environment. Part 1: Selecting a Key Size for Your Root Certificate Server in Windows Server 2012 AD CS. Part 2: Selecting a Cryptographic Key Provider in Windows Server 2012 AD CS. In this post, we’ll look at the time involved to generate asymmetric key pars.
When it comes to the word ‘Encryption,’ we think of it as a technique that protects data using a cryptographic key, and there’s nothing wrong with this. However, what most people don’t realize is that there are certain types of encryption methods. Asymmetric Encryption, also known as Public-Key Cryptography, is an example of one type.
Unlike “normal” (symmetric) encryption, Asymmetric Encryption encrypts and decrypts the data using two separate yet mathematically connected cryptographic keys. These keys are known as a ‘Public Key’ and a ‘Private Key.’ Together, they’re called a ‘Public and Private Key Pair.’
Let’s see how these two keys work together to create the formidable force that is Asymmetric Encryption.
How does Asymmetric Encryption work?
Asymmetric Encryption uses two distinct, yet related keys. One key, the Public Key, is used for encryption and the other, the Private Key, is for decryption. As implied in the name, the Private Key is intended to be private so that only the authenticated recipient can decrypt the message.
Let’s understand this with a simple asymmetric encryption example.
Pretend you’re a spy agency and you need to devise a mechanism for your agents to report in securely. You don’t need two-way communication, they have their orders, you just need regular detailed reports coming in from them. Asymmetric encryption would allow you to create public keys for the agents to encrypt their information and a private key back at headquarters that is the only way to decrypt it all. This provides an impenetrable form of one-way communication.
How are the two keys generated?
At the heart of Asymmetric Encryption lies a cryptographic algorithm. This algorithm uses a key generation protocol (a kind of mathematical function) to generate a key pair. Both the keys are mathematically connected with each other. This relationship between the keys differs from one algorithm to another.
The algorithm is basically a combination of two functions – encryption function and decryption function. To state the obvious, the encryption function encrypts the data and decryption function decrypts it.
This is how Asymmetric Encryption is used in SSL/TLS certificates
In SSL/TLS and other digital certificates, both methods – Symmetric and Asymmetric – are employed. Now, you might be wondering, ‘Why both? Shouldn’t Asymmetric cryptography be used as it’s more secure?’ Granted, it is more secure, but it comes with a pitfall. A major drawback when it comes to Public Key Cryptography is the computational time. As the verification and functions are applied from both the sides, it slows down the process significantly. That’s where Symmetric Encryption comes and saves the day.
First, when two parties (browser and server in the case of SSL) come across each other, they validate each other’s private and public key through Asymmetric Encryption. Once the verification is successful and both know whom they’re talking to, the encryption of the data starts – through Symmetric Encryption. Thereby saving significant time and serving the purposes of confidentiality and cellspacing='0' cellpadding='0'>Symmetric EncryptionAsymmetric EncryptionSymmetric encryption consists of one of key for encryption and decryption.Asymmetric Encryption consists of two cryptographic keys known as Public Key and Private Key.Symmetric Encryption is a lot quicker compared to the Asymmetric method.As Asymmetric Encryption incorporates two separate keys, the process is slowed down considerably.RC4RSAAESDiffie-HellmanDESECC3DESEl GamalQUADDSA
You’re using Asymmetric Encryption without even realizing it
When you visit any HTTPS website/webpage, your browser establishes Asymmetrically encrypted connection with that website. Your browser automatically derives the public key of the SSL/TLS certificate installed on the website (that’s why it’s called ‘Public Key’). Do you want to see what it looks like? Click the green padlock you see in front of our URL, and go to certificate details. This is how it’ll look like:
30 82 01 0a 02 82 01 01 00 c2 d8 be ec a4 e1 52 20 7f 7f 7d 1a 17 38 99 17 ef 6a 9e af 66 89 67 5a 58 e2 b8 7c 76 f2 b8 c6 8f 98 e4 06 eb 3c 1c 04 34 1e 10 a9 42 c2 34 be 99 3b 98 7b 35 60 3a d5 41 bb 96 19 1a 3c 66 a0 75 77 64 2a 2e 19 42 5a b1 d0 1f 4d ac 32 2e af 4e 20 b8 89 07 83 51 21 e4 35 02 4b 10 45 03 37 ce 26 87 e0 b8 4d dc ba c5 e7 ae 60 68 b3 0c a3 5c 4f dd 30 1f 95 96 a5 2e e5 6f ae e8 e2 dc df 3a ab 51 74 82 f5 9e 15 3a ab 7c 99 3c 07 5b ad f2 88 a2 23 1c cd 41 d8 66 a4 90 0d 4a 23 05 5c de aa e3 82 13 f4 08 87 b3 34 08 6f 38 fb f8 84 ec 06 99 e0 ab 8a ab 1b 7c 99 fd 57 94 67 17 15 b7 27 67 c1 bc d1 a7 f6 c6 7e 01 63 02 0c 03 c4 bb 1f 70 0d db 27 ab 79 57 d9 92 35 f3 92 3c ad f4 fb f0 36 82 33 5a a0 f9 82 78 04 a6 e7 d6 ee 01 23 68 36 68 3b 41 fe 68 56 0b 6b 36 3b 83 b1 02 03 01 00 01
Amazing isn’t it?
So, this key encrypts any information you send to our website during the initial handshake, and our Private Key will decrypt it. Do you want to see what our Private Key looks like? Here it is:
Oh wait, that’s the key to our office. Did we tell you that the Private Key is supposed to be “Private?” Yes, you should NEVER EVER give it to anyone and keep it close to your chest (not literally). We recommend storing it at a location where only authorized people have access to it. If possible, you should try and save it on a hardware device that’s not connected to your system all the time.

Concluding Words About Asymmetric Cryptography
What Generates The Key Pair Used In Asymmetric Cryptography In Math
Still here? Good. We believe that now you (hopefully) know what Asymmetric Encryption is and how it protects you from the wrath of cybercriminals. If you have a website and want to protect it with the same technology.
Buy SSL Certificates and Save Up to 89%
Secure a website with HTTPS in a minutes. We offers trusted SSL brands SSL Certificates like DV SSL, EV SSL, OV SSL, Wildcard SSL, and Multi-Domain SAN SSL Certificates.
Buy SSL Certificates at Only $5.45
Related Resources
- Cryptography Tutorial
- Cryptography Useful Resources
- Selected Reading
Public Key Cryptography
Unlike symmetric key cryptography, we do not find historical use of public-key cryptography. It is a relatively new concept.
Symmetric cryptography was well suited for organizations such as governments, military, and big financial corporations were involved in the classified communication.
With the spread of more unsecure computer networks in last few decades, a genuine need was felt to use cryptography at larger scale. The symmetric key was found to be non-practical due to challenges it faced for key management. This gave rise to the public key cryptosystems.
The process of encryption and decryption is depicted in the following illustration −
The most important properties of public key encryption scheme are −
Different keys are used for encryption and decryption. This is a property which set this scheme different than symmetric encryption scheme.
Each receiver possesses a unique decryption key, generally referred to as his private key.
Receiver needs to publish an encryption key, referred to as his public key.
Some assurance of the authenticity of a public key is needed in this scheme to avoid spoofing by adversary as the receiver. Generally, this type of cryptosystem involves trusted third party which certifies that a particular public key belongs to a specific person or entity only.
Encryption algorithm is complex enough to prohibit attacker from deducing the plaintext from the ciphertext and the encryption (public) key.
Though private and public keys are related mathematically, it is not be feasible to calculate the private key from the public key. In fact, intelligent part of any public-key cryptosystem is in designing a relationship between two keys.
There are three types of Public Key Encryption schemes. We discuss them in following sections −
Google Sketchup Pro is a influential engine. It is a powerful program withaffection to 3D CAD making and design allows planners, engineers andconstructors to generate remarkable 3D designs in structures, building andengineering. Key generator for google sketchup 2015 32 bit.
RSA Cryptosystem
This cryptosystem is one the initial system. It remains most employed cryptosystem even today. The system was invented by three scholars Ron Rivest, Adi Shamir, and Len Adleman and hence, it is termed as RSA cryptosystem.
We will see two aspects of the RSA cryptosystem, firstly generation of key pair and secondly encryption-decryption algorithms.
Generation of RSA Key Pair
Each person or a party who desires to participate in communication using encryption needs to generate a pair of keys, namely public key and private key. The process followed in the generation of keys is described below −
Generate the RSA modulus (n)
Select two large primes, p and q.
Calculate n=p*q. For strong unbreakable encryption, let n be a large number, typically a minimum of 512 bits.
Find Derived Number (e)
Number e must be greater than 1 and less than (p − 1)(q − 1).
There must be no common factor for e and (p − 1)(q − 1) except for 1. In other words two numbers e and (p – 1)(q – 1) are coprime.
Form the public key
The pair of numbers (n, e) form the RSA public key and is made public.
Interestingly, though n is part of the public key, difficulty in factorizing a large prime number ensures that attacker cannot find in finite time the two primes (p & q) used to obtain n. This is strength of RSA.
Generate the private key
Private Key d is calculated from p, q, and e. For given n and e, there is unique number d.
Number d is the inverse of e modulo (p - 1)(q – 1). This means that d is the number less than (p - 1)(q - 1) such that when multiplied by e, it is equal to 1 modulo (p - 1)(q - 1).
This relationship is written mathematically as follows −
The Extended Euclidean Algorithm takes p, q, and e as input and gives d as output.
Example
An example of generating RSA Key pair is given below. (For ease of understanding, the primes p & q taken here are small values. Practically, these values are very high).
Let two primes be p = 7 and q = 13. Thus, modulus n = pq = 7 x 13 = 91.
Select e = 5, which is a valid choice since there is no number that is common factor of 5 and (p − 1)(q − 1) = 6 × 12 = 72, except for 1.
The pair of numbers (n, e) = (91, 5) forms the public key and can be made available to anyone whom we wish to be able to send us encrypted messages.
Input p = 7, q = 13, and e = 5 to the Extended Euclidean Algorithm. The output will be d = 29.
Check that the d calculated is correct by computing −
Hence, public key is (91, 5) and private keys is (91, 29).
Encryption and Decryption
Once the key pair has been generated, the process of encryption and decryption are relatively straightforward and computationally easy.
Interestingly, RSA does not directly operate on strings of bits as in case of symmetric key encryption. It operates on numbers modulo n. Hence, it is necessary to represent the plaintext as a series of numbers less than n.
RSA Encryption
Suppose the sender wish to send some text message to someone whose public key is (n, e).
The sender then represents the plaintext as a series of numbers less than n.
To encrypt the first plaintext P, which is a number modulo n. The encryption process is simple mathematical step as −
In other words, the ciphertext C is equal to the plaintext P multiplied by itself e times and then reduced modulo n. This means that C is also a number less than n.
Returning to our Key Generation example with plaintext P = 10, we get ciphertext C −
RSA Decryption
The decryption process for RSA is also very straightforward. Suppose that the receiver of public-key pair (n, e) has received a ciphertext C.
Receiver raises C to the power of his private key d. The result modulo n will be the plaintext P.
Returning again to our numerical example, the ciphertext C = 82 would get decrypted to number 10 using private key 29 −
What Generates The Key Pair Used In Asymmetric Cryptography Theory
RSA Analysis
The security of RSA depends on the strengths of two separate functions. The RSA cryptosystem is most popular public-key cryptosystem strength of which is based on the practical difficulty of factoring the very large numbers.
Encryption Function − It is considered as a one-way function of converting plaintext into ciphertext and it can be reversed only with the knowledge of private key d.
Key Generation − The difficulty of determining a private key from an RSA public key is equivalent to factoring the modulus n. An attacker thus cannot use knowledge of an RSA public key to determine an RSA private key unless he can factor n. It is also a one way function, going from p & q values to modulus n is easy but reverse is not possible.
If either of these two functions are proved non one-way, then RSA will be broken. In fact, if a technique for factoring efficiently is developed then RSA will no longer be safe.
The strength of RSA encryption drastically goes down against attacks if the number p and q are not large primes and/ or chosen public key e is a small number.
ElGamal Cryptosystem
Along with RSA, there are other public-key cryptosystems proposed. Many of them are based on different versions of the Discrete Logarithm Problem.
ElGamal cryptosystem, called Elliptic Curve Variant, is based on the Discrete Logarithm Problem. It derives the strength from the assumption that the discrete logarithms cannot be found in practical time frame for a given number, while the inverse operation of the power can be computed efficiently.
Let us go through a simple version of ElGamal that works with numbers modulo p. In the case of elliptic curve variants, it is based on quite different number systems.
Generation of ElGamal Key Pair
Each user of ElGamal cryptosystem generates the key pair through as follows −
Choosing a large prime p. Generally a prime number of 1024 to 2048 bits length is chosen.
Choosing a generator element g.
This number must be between 1 and p − 1, but cannot be any number.
It is a generator of the multiplicative group of integers modulo p. This means for every integer m co-prime to p, there is an integer k such that gk=a mod n.
For example, 3 is generator of group 5 (Z5 = {1, 2, 3, 4}).
| N | 3n | 3n mod 5 |
|---|---|---|
| 1 | 3 | 3 |
| 2 | 9 | 4 |
| 3 | 27 | 2 |
| 4 | 81 | 1 |
Choosing the private key. The private key x is any number bigger than 1 and smaller than p−1.
Computing part of the public key. The value y is computed from the parameters p, g and the private key x as follows −
Obtaining Public key. The ElGamal public key consists of the three parameters (p, g, y).
For example, suppose that p = 17 and that g = 6 (It can be confirmed that 6 is a generator of group Z17). The private key x can be any number bigger than 1 and smaller than 71, so we choose x = 5. The value y is then computed as follows −
Thus the private key is 62 and the public key is (17, 6, 7).
Encryption and Decryption
The generation of an ElGamal key pair is comparatively simpler than the equivalent process for RSA. But the encryption and decryption are slightly more complex than RSA.
ElGamal Encryption
Suppose sender wishes to send a plaintext to someone whose ElGamal public key is (p, g, y), then −
Sender represents the plaintext as a series of numbers modulo p.
To encrypt the first plaintext P, which is represented as a number modulo p. The encryption process to obtain the ciphertext C is as follows −
- Randomly generate a number k;
- Compute two values C1 and C2, where −
Send the ciphertext C, consisting of the two separate values (C1, C2), sent together.
Referring to our ElGamal key generation example given above, the plaintext P = 13 is encrypted as follows −
- Randomly generate a number, say k = 10
- Compute the two values C1 and C2, where −
Send the ciphertext C = (C1, C2) = (15, 9).
ElGamal Decryption
To decrypt the ciphertext (C1, C2) using private key x, the following two steps are taken −
Compute the modular inverse of (C1)x modulo p, which is (C1)-x , generally referred to as decryption factor.
Obtain the plaintext by using the following formula −
In our example, to decrypt the ciphertext C = (C1, C2) = (15, 9) using private key x = 5, the decryption factor is
Extract plaintext P = (9 × 9) mod 17 = 13.
ElGamal Analysis
In ElGamal system, each user has a private key x. and has three components of public key − prime modulus p, generator g, and public Y = gx mod p. The strength of the ElGamal is based on the difficulty of discrete logarithm problem.
The secure key size is generally > 1024 bits. Today even 2048 bits long key are used. On the processing speed front, Elgamal is quite slow, it is used mainly for key authentication protocols. Due to higher processing efficiency, Elliptic Curve variants of ElGamal are becoming increasingly popular.
Elliptic Curve Cryptography (ECC)
Elliptic Curve Cryptography (ECC) is a term used to describe a suite of cryptographic tools and protocols whose security is based on special versions of the discrete logarithm problem. It does not use numbers modulo p.
ECC is based on sets of numbers that are associated with mathematical objects called elliptic curves. There are rules for adding and computing multiples of these numbers, just as there are for numbers modulo p.
ECC includes a variants of many cryptographic schemes that were initially designed for modular numbers such as ElGamal encryption and Digital Signature Algorithm.
It is believed that the discrete logarithm problem is much harder when applied to points on an elliptic curve. This prompts switching from numbers modulo p to points on an elliptic curve. Also an equivalent security level can be obtained with shorter keys if we use elliptic curve-based variants.
The shorter keys result in two benefits −
- Ease of key management
- Efficient computation
These benefits make elliptic-curve-based variants of encryption scheme highly attractive for application where computing resources are constrained.
RSA and ElGamal Schemes – A Comparison
Let us briefly compare the RSA and ElGamal schemes on the various aspects.
| RSA | ElGamal |
|---|---|
| It is more efficient for encryption. | It is more efficient for decryption. |
| It is less efficient for decryption. | It is more efficient for decryption. |
| For a particular security level, lengthy keys are required in RSA. | For the same level of security, very short keys are required. |
| It is widely accepted and used. | It is new and not very popular in market. |