Playing Cards Generating Keys Encryption
- Playing Cards Generating Keys Encryption For Windows 10
- Playing Cards Generating Keys Encryption Download
If you are using encryption to exchange data then you will need a key exchange protocol, but you don't make one yourself instead use one off-the-shelf like TLS or SSL. If you use encryption to store data then you generate the IV using CryptGenRandom (or its.net equivalent RandomNumberGenerator.GetBytes ) and save it along the document (in clear, no need to protect the IV). Pocket-RC4 22 and Solitaire 26 each use a deck of playing cards to generate a keystream, which is then added to the plaintext to get the ciphertext. Fortuitously, a standard card deck has exactly twice as many cards as there are English letters, so representing letters with cards is espe-cially easy.
- If the target device is too weak/underpowered to generate the keys, it is also too weak to use asymmetric encryption (this includes entropy sources). Of course, there are memory-constrained hardwired devices (smart cards, for instance), but you can use a physically secure link to move the keys into them without being connected to the Internet.
- A friend of mine suggested that I use random.org to generate 128 bit (16 byte) WEP keys for 802.11a or 802.11b wireless cards. Test of Encryption Routines. From: Randy Tate Date: 30 April 2003 I'm using the random number to help me create block ciphers for custom encryption routines.
Playing Cards Generating Keys Encryption For Windows 10
What is Credit Card Encryption?
Playing Cards Generating Keys Encryption Download

Credit card encryption is a security measure used to reduce the likelihood of a credit or debit card information being stolen. Credit card encryption involves both the security of the card, the security of the terminal where a card is scanned, and the security of the transmission of the card’s information between the terminal and a back-end computer system.
Understanding Credit Card Encryption
Credit cards are an integral part of the payment process. Consumers expect that most businesses will accept cards as a method of payment, rather than relying on cash to conduct transactions. Businesses provide electronic terminals that a consumer can scan his or her credit card through, with the terminals sending the card’s identifying information to computer servers in order to verify that the consumer has sufficient funds.
How Credit Card Encryption Works
When a credit account holder makes a purchase with their card, the information such as the account number is scrambled by an algorithm. The intent is to make it impossible to access that information without the corresponding encryption key that lets the merchant and financial institution conduct their transactions. Until the information is decrypted by the key, the information is not usable, making it safe so long as it remains unlocked.
Because credit cards require the use of an electronic transfer of information, they can be exposed to third parties who can steal the card’s information. Types of fraud include skimming, carding, and RAM scraping.
Card issuers use a variety of methods to encrypt credit cards. The magnetic strip on the back of a card is typically encrypted and can only be read by a card scanner. Relying solely on the magnetic strip is a less secure method than requiring the use of a PIN-and-chip, because a PIN makes it more difficult for stolen credit cards to be authorized and used. A smart card with an electronic chip adds can be harder for thieves and hackers to steal information from, compared with other forms of encryption and security put in place to protect cred account information.
For transactions that do not require a card to be scanned, such as an online transaction or in-app purchase, websites require both the credit card number on the front of the card and a CVV number located on the back of the card to be used. Using a CVV prevents an individual from being able to use only a stolen credit card number to conduct a transaction.
Key Takeaways
- Credit card encryption is a security measure used to reduce the likelihood of a credit or debit card information being stolen
- It makes it impossible to access the credit card information without the corresponding encryption key that lets the merchant and financial institution conduct their transactions.
- Card issuers use many methods to encrypt credit cards including magnetic strips, PIN numbers, electronic chips and a CVV in case of online transactions.
Creating and managing keys is an important part of the cryptographic process. Symmetric algorithms require the creation of a key and an initialization vector (IV). The key must be kept secret from anyone who should not decrypt your data. The IV does not have to be secret, but should be changed for each session. Asymmetric algorithms require the creation of a public key and a private key. The public key can be made public to anyone, while the private key must known only by the party who will decrypt the data encrypted with the public key. This section describes how to generate and manage keys for both symmetric and asymmetric algorithms.

Symmetric Keys
The symmetric encryption classes supplied by the .NET Framework require a key and a new initialization vector (IV) to encrypt and decrypt data. Whenever you create a new instance of one of the managed symmetric cryptographic classes using the parameterless constructor, a new key and IV are automatically created. Anyone that you allow to decrypt your data must possess the same key and IV and use the same algorithm. Generally, a new key and IV should be created for every session, and neither the key nor IV should be stored for use in a later session.
To communicate a symmetric key and IV to a remote party, you would usually encrypt the symmetric key by using asymmetric encryption. Sending the key across an insecure network without encrypting it is unsafe, because anyone who intercepts the key and IV can then decrypt your data. For more information about exchanging data by using encryption, see Creating a Cryptographic Scheme.
The following example shows the creation of a new instance of the TripleDESCryptoServiceProvider class that implements the TripleDES algorithm.
When the previous code is executed, a new key and IV are generated and placed in the Key and IV properties, respectively.
Sometimes you might need to generate multiple keys. In this situation, you can create a new instance of a class that implements a symmetric algorithm and then create a new key and IV by calling the GenerateKey and GenerateIV methods. The following code example illustrates how to create new keys and IVs after a new instance of the symmetric cryptographic class has been made.
When the previous code is executed, a key and IV are generated when the new instance of TripleDESCryptoServiceProvider is made. Another key and IV are created when the GenerateKey and GenerateIV methods are called.
Asymmetric Keys
The .NET Framework provides the RSACryptoServiceProvider and DSACryptoServiceProvider classes for asymmetric encryption. These classes create a public/private key pair when you use the parameterless constructor to create a new instance. X force key generator for autocad 2014 download. Asymmetric keys can be either stored for use in multiple sessions or generated for one session only. While the public key can be made generally available, the private key should be closely guarded.
A public/private key pair is generated whenever a new instance of an asymmetric algorithm class is created. After a new instance of the class is created, the key information can be extracted using one of two methods:
The ToXmlString method, which returns an XML representation of the key information.
The ExportParameters method, which returns an RSAParameters structure that holds the key information.
Both methods accept a Boolean value that indicates whether to return only the public key information or to return both the public-key and the private-key information. An RSACryptoServiceProvider class can be initialized to the value of an RSAParameters structure by using the ImportParameters method.
Launching TerminalTerminal is an application that comes with macOS and provides you with an interface to run text commands, switch through folders, and manage files. 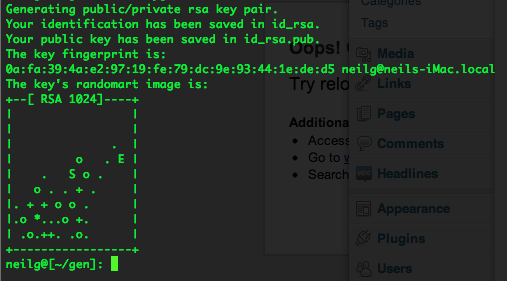 When it asks for a pass phrase, make sure to set a strong pass phrase for the key. First make sure you are in your home directory: cd /and then generate the keypair with: ssh-keygen -t rsaIt will ask for location, just accept the default location ( /.ssh/idrsa.pub) by pressing Return. You can usually find it in your Applications → Utilities folder. Generating a key pairType these commands in your Terminal window and press Return.
When it asks for a pass phrase, make sure to set a strong pass phrase for the key. First make sure you are in your home directory: cd /and then generate the keypair with: ssh-keygen -t rsaIt will ask for location, just accept the default location ( /.ssh/idrsa.pub) by pressing Return. You can usually find it in your Applications → Utilities folder. Generating a key pairType these commands in your Terminal window and press Return.
Asymmetric private keys should never be stored verbatim or in plain text on the local computer. If you need to store a private key, you should use a key container. For more on how to store a private key in a key container, see How to: Store Asymmetric Keys in a Key Container.
The following code example creates a new instance of the RSACryptoServiceProvider class, creating a public/private key pair, and saves the public key information to an RSAParameters structure.